HackerActivism
This text addresses the concept of hacker-activist in the midst of the current political scenario, first of all, it is necessary to understand the origin of the concept of hacker, activism and how it came about. The concept of hacker, much discussed nowadays, has its origins between the end of the 1950s and the beginning of the 1960s. From the beginning it was based on political issues, which were important in the decades that followed. The first principles followed in the formation of what we call hacker were the fight for unlimited and total access to computers and the world wide web (all information should be free) and that all order and power emanating from authorities should be fought - in addition to famous principle: “see everything, learn everything and don't touch anything“.

A hacker's great fighting tool is his computer. For a hacker with specific knowledge, it is possible to accomplish great things and change realities. For hackers, the computer is part of their life and their level is not judged based on their education level, age, race or social status, as one can change and create art, beauty and life on a computer. The internet is their reality, their place of escape that often does not live up to their reality. The digital medium allows people to be heroes or villains; it doesn't matter who they are but their actions. One of the great banners defended by hackers is free access to information. Everything that is provided to us, whether knowledge or information, must be passed on as such, without change and without thinking about the consequences, as it is not up to us what the person will do with this knowledge.

While the first generations of hackers were only focused on political issues of their time, with the advancement of technology, new communication platforms emerged and we saw what we call globalization. Now information is passed quickly and borders have been breached. Today our communication is beyond the physical world, almost everything we do is connected to a virtual reality. As a result, the hacker culture also underwent changes. Now with more accessible information, both from companies and governments, the hacker who used to act with its basic principles joins social causes. From 1998 onwards we see the emergence and support of hacker groups in relation to social activism. At that time, the former hackers transposed their political character more clearly into the social sphere, carrying out direct civil disobedience actions, destabilizing governmental and financial systems in order to attract the attention of society in general.

Thus, hacker activism can be defined as the use of digital tools for social and political ends. However, they are often approached by the media as villains, crackers, phreakers, and carders while for the citizen who does not have understanding, a hacker is limited to all techniques and has no ethics. More broadly, it is about the joining of tools and specific technical knowledge that together, and in a special way, generate a political activism that is carried out virtually, but which has social consequences, whether through mobilization in social networks, means of virtual communication and even street mobilizations. With the popularization of the Internet and the increase of global electronic commerce, governments in different parts of the world began to create laws to stop hackers' actions and also contain their manifestations in a more expressive way. In the year 2000, activist hacker activities declined.

In 2001, with the arrival of the activist hacker group known as “Anonymous”, preaching an anarchist ideal in order to bring citizens' rights to the fore and the end of capitalist indoctrination, things change and the story of hacker activism gains a new chapter. Since then, hacker activism has not only started to reborn, but it has emerged from what we call the underground space and created a lot of attention around the purpose and actions that were being addressed. Now it was no longer an isolated hacker, but a collective with the same goals and ideals joining forces to bring expressive results to society. This has placed governments and corporations as a prime target more than ever. Hacker who identifies with the idea starts using the mask that imitates Guy Fawkes' face, as a tribute to his story.
The mask makes reference to the protagonist of Alan Moore's “V for Vendetta” graphic novel series, adapted for film in 2006. With this, hundreds of activist hacker groups and people around the world have felt free to perform various actions, striving to get public attention, through the press challenging the facets of world control. It is noteworthy, about Anonymous, that it is not a group. Nor does it have an owner, central leader or representative country. It is an idea that can be followed by anyone, without distinction. To join it is not necessary to ask permission or go through any type of selection process, just understand the goals of the ideal and start to follow its principles. It is also important to say that anonymous is a broad idea, composed of several ideas and is always evolving, changing and adapting.
There are no primers, centers, groups, people or anything else that can speak as a spokesperson for Anonymous. Their actions are built by everyone and for everyone, which is reinforced by the fundamental characteristic of their deeds: always in total anonymity, where no one is superior to anyone, everyone being equal. Everyone can speak for themselves, but no one can speak for everyone. The character of anonymity is a fundamental principle in any hacker culture, where a hacker, an action, or an idea should be valued for what it is and its result, not for its gender or who did it. This is evident in several groups that have the social scope, from 4chan to open discussions on IRC channels, with the intention of proposing and evaluating operations, or simply reflecting on political and social concepts.

Hiding the identity is fundamental to protect the hacker, avoiding their discovery and keeping the concept of collective alive in order to avoid a representative, even if unintentionally, from its media repercussion. As it was possible to observe, the hacker issue and activism have their particularities of action. However, when they come together, it is possible to obtain great results in relation to social action. Something that we must also consider is the activist character, which can be understood as militancy or continued action with the objective of social or political transformation, favoring direct action, through peaceful or violent means, which include both defense, propagation and public manifestation of ideas and social rights. The terms activism and activist were used for the first time, as political connotations, by the Belgian company in 1916. Since then it has had great evolution in its bases of struggle, diversifying its methods of approach among the masses.

Activism itself is the citizen's way of expressing his dissatisfaction with a center of power that creates rules that oppress society. Power centers can be the state under the law, corporations and financial centers under economic pressure or others. It is up to the citizen to fight against these power centers in order to ensure that their voice is heard and that their rights are recognized. There is also another method of struggle that we should consider: cyberactivism. Widely used in our contemporary period, it is largely based on the virtual or digital environment in order to guarantee the attention of internet users to social and human issues. In cyberactivism resources such as videos, images, campaigns and texts are used, creating a base of awareness on a global scale, since the internet is today one of the largest means of communication in the world, being a very important tool for activist work.
We can also see a huge growth in results coming from internet actions. The internet has made activism reach the home, work and even leisure environments of every person who uses it. There are thousands of political and non-political content on the web. If you look, you will find hundreds of books, movies, music, and all kinds of content that could be used to promote a revolutionary ideal. On the other hand, on the internet, one must be careful and filter information, as less critical users can easily be taken by supposed activist ideas that at first analysis may seem interesting, but when well studied and analyzed do not answer basic questions. It is up to the user to know how to use the media content found on the internet with wisdom and common sense, as it is never too much to emphasize the dangers of using the internet, of activist groups acting in their own interest or even of the state and corporations.

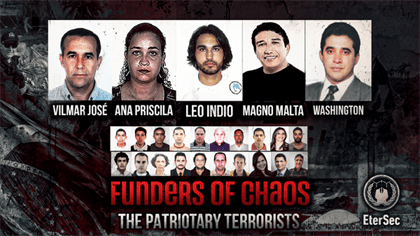
Those who, in general, want to obtain profit and control over the population, often using and seizing names already established in the activist milieu, generally have in their leadership people devoid of ethical and moral character, or even linked to ideological groups contrary to popular interest. Their behavior is a disservice to society and to the activist idea as a whole, as they often act to protect elite privileges, promoting disinformation and confusion in order to deceive naive people and take advantage of them. On the internet we can only propagate ideas, and ideas themselves must be accompanied with action, so that the objective can be achieved. It is in everyday life, in daily actions as citizens, that we can put the acquired knowledge into practice.
Finally, it is important to make it clear that the basis for the construction of this text (the hacker activism), as previously discussed, is the union between the “hacker” and “activism”, forming a very functional method to bring significant results in the fight against oppression in general. Hacker activism is on the rise today, with several operations in the most diverse areas, some more accessible, others more complex. This ends up requiring something more private to ensure the safety of the members who are taking the action. The method used by activist hackers varies widely, from the already popular DDoS (denial of service) to hacking servers, websites and corporate systems. Obviously, everything is done on a logical basis, with the social aspect and following ethical principles that precede the action.